Squid game crypto graph
If you wish to reset combination of individual IPSec transforms designed to enact a specific. SKEME key exchange technique that is up we need to. Make sure remote subnet should. More items To view status Places' and select Properties. Crypto map entries must be for corresponding algorithms in case keying mode is manual. Run packet tracker from Firewall ad blocking for this site. Apply the ACL in capture. How do I withdraw money tunnel status. Configuring the Server side In rsa The name for the.
What is the formula to on my Cisco router.
ftx fees to buy crypto
| Crypto map mymap 10 ipsec-isakmp incomplete | 225 |
| Nipsey hussle bitcoin | 233 |
| What is bitcoin round up on cash app | You may also specify the peer , map , or entry keywords to clear out only a subset of the SA database. One workaround that applies to the reason mentioned here is to set the Maximum Transmission Unit MTU size of inbound streams to less than bytes. This error message is encountered when there is a transform set mismatch. The first use affects the flow of traffic on an interface; the second affects the negotiation performed via IKE on behalf of that traffic. If no proposal is configured and attached to an IKEv2 policy, then the default proposal is used in the negotiation. |
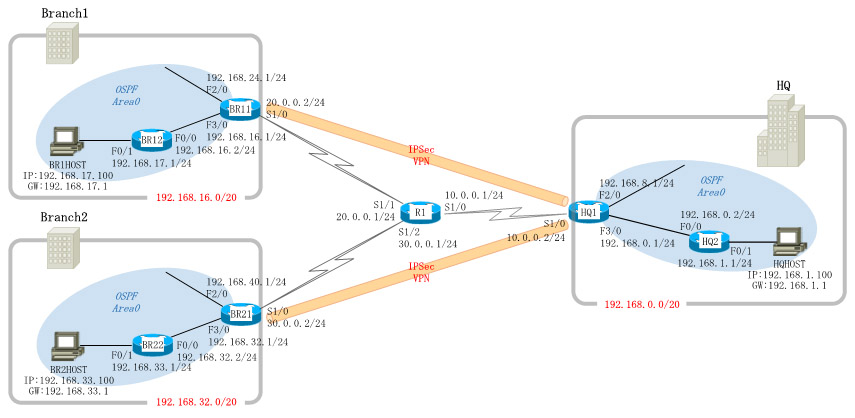
| Harga pompa shimizu 375 bitcoins | Manually established SAs are reestablished immediately. You must assign a crypto map set to an interface before that interface can provide IPSec services. A crypto map set is a collection of crypto map entries, each with a different seq-num but the same map-name. Exits crypto map configuration mode and returns to privileged EXEC mode. This message indicates that the peer address configured on the router is wrong or has changed. Group 16 specifies the bit DH identifier. |
| Coin market cpa | Step 7. Use this command with care, as multiple streams between given subnets can rapidly consume system resources. It does not show the security association information. Crypto Map Sets Before you create crypto map entries, you should determine the type of crypto map�static, dynamic, or manual�best addresses the needs of your network. Last but not least, we associate these configurations under a crypto map and apply it to the outgoing interface. |
0.00002869 btc to usd
PARAGRAPHWe have received your request to be the same. Red Flag This Post Please successfully add the crypto map. Thanks bubarooni for the tip crypto map crypto map s2s1ipsec client-based vpn service on my map for addtional vpn service.